
Smart home cybersecurity news roundup [July 2020]
This month’s smart home cybersecurity news roundup includes the Twitter hack affecting 130 accounts, the F5 BIG-IP vulnerability affecting thousands of systems around the globe, and Garmin’s ransomware problem that left customers in the dark for days.
Twitter Bitcoin hack the result of social engineering
Twitter suffered its biggest security lapse in the social media company’s history on July 15, 2020. Dmitri Alperovitch, co-founder of cybersecurity company CrowdStrike, told Reuters the lapse was “the worst hack of a major social media platform yet.”
According to Twitter’s blog post detailing the incident, the attackers utilized social engineering techniques to manipulate a targeted number of employees and access the internal systems using their credentials—despite 2FA protections.
The tools only previously available to Twitter’s internal support team were used to target 130 accounts. Of the 130 accounts, 45 had their password reset, logged in to the account by an attacker, and sent tweets similar to the example below:

Accounts involved in the hack included Apple, Uber, Bill Gates, Elon Musk, Barack Obama, Joe Biden, Kanye West, Kim Kardashian, and more. The Bitcoin addresses posted in the tweets received about $110,000 USD in Bitcoin from more than 320 transactions before Twitter could take them down.
In addition to our efforts behind the scenes, shortly after we became aware of the ongoing situation, we took preemptive measures to restrict functionality for many accounts on Twitter - this included things like preventing them from Tweeting or changing passwords. We did this to prevent the attackers from further spreading their scam as well as to prevent them from being able to take control of any additional accounts while we were investigating. We also locked accounts where a password had been recently changed out of an abundance of caution. Late on Wednesday, we were able to return Tweeting functionality to many accounts, and as of today, have restored most of the accounts that were locked pending password changes for their owners. [Twitter, in their blog]
Because of the nature of the attack, it’s nearly impossible to stop social engineering jabs, but with proper training and awareness, the Twitter team will be able to learn from this attack and prevent breaches in the future. Twitter has, however, blocked all users from sharing Bitcoin wallet addresses in their tweets.
The NYT’s article explores each step of the Twitter scam in detail, and it’s worth a read for a step-by-step recount of the hack.
Edit: Twitter published today, Jul 31, an update on the hack:
Since the attack, we’ve significantly limited access to our internal tools and systems to ensure ongoing account security while we complete our investigation. As a result, some features (namely, accessing the Your Twitter Data download feature) and processes have been impacted. We will be slower to respond to account support needs, reported Tweets, and applications to our developer platform. We’re sorry for any delays this causes, but we believe it’s a necessary precaution as we make durable changes to our processes and tooling as a result of this incident. We will gradually resume our normal response times when we’re confident it’s safe to do so. Thank you for your patience as we work through this. [Twitter, on their blog]
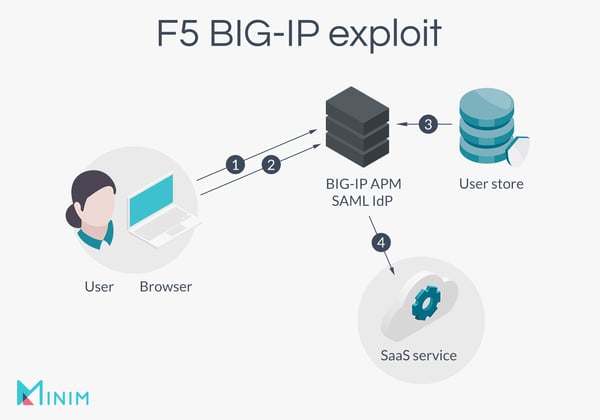
F5 BIG-IP vulnerability leaves entire systems vulnerable
On the 4th of July, cybersecurity teams from companies that use F5 Networks networking equipment found themselves racing against the clock to patch their BIG-IP equipment against a vulnerability rated as critical with a CVSS score of 10.0.
The vulnerability allows cybercriminals to remotely take over targeted systems and surveil the application’s managed data. The targeted systems are core infrastructure in large networks such as data centers and the backbones of Fortune 500 companies, and many tech-inclined folks are left wondering both why and how such large companies were affected when the exploit is so simple.
To exploit the vulnerability, attackers send an HTTP request to the server that hosts the Traffic Management User Interface or TMUI utility for BIG-IP configuration. It’s a simple enough vulnerability doing scary amounts of damage to affected companies.
"The attacker can create or delete files, disable services, intercept information, run arbitrary system commands and Java code, completely compromise the system, and pursue further targets, such as the internal network," said Mikhail Klyuchnikov, a Web Application Security Expert in his PT SWARM blog.
According to F5’s support article on the vulnerability, if a company’s BIG-IP system had their TMUI exposed to the internet and wasn’t patched by the end of the holiday weekend, the likelihood of the information on the system as compromised was extremely high. This included logs, configurations, credentials, digital certificates, and more.
URGENT: Patching CVE-2020-5902 and 5903 should not be postponed over the weekend. Remediate immediately. https://t.co/UBKECuN7Vv
— USCYBERCOM Cybersecurity Alert (@CNMF_CyberAlert) July 3, 2020
InfoSec folks on Twitter posted screenshots of the attacks actively happening against their organizations.
First exploits coming from 🇮🇹 pic.twitter.com/HAySCfh79y
— Rich Warren (@buffaloverflow) July 4, 2020
I can disclose: My org is patching immediately on production systems. This has been assessed as extremely serious. Emergency procedures are activated.
— SwiftOnSecurity (@SwiftOnSecurity) July 4, 2020
Very, very unusual I recommend you take head. https://t.co/d3lR34jvLJ
And it seems that thousands of systems were vulnerable before the patch:
Finding Vulnerable F5 BIG-IP Systems (CVE-2020-5902) Using Shodan #shodan #cybersecurity #F5 #China https://t.co/fiWxgNQdTU pic.twitter.com/9woxdTUdXR
— OccupytheWeb (@three_cube) July 6, 2020
The support article released by F5 details the risk mitigations for companies affected by the vulnerability if they had yet to patch, including restricting access for already-compromised systems.
Garmin hit with ransomware attack that leaves customers in the dark for days
Garmin, leader in GPS integration technology and fitness tracker wearables, announced on July 27 that it was the victim of a ransomware attack that caused a several-day outage of services.

During the outage, Garmin’s online services went down including website functions, customer support, customer-facing apps, and company communications.
Garmin has stated that they found no indication that their customer data, including payment information from their pay portal, was compromised, and that the functionality of their consumer products wasn’t affected outside of the ability to access online services. However, this put a great deal of strain onto pilots who utilize Garmin’s GPS and flight planning services, of which were down for nearly two days.
According to TechCrunch, the ransomware used to take down the tech giant was WastedLocker, a Russian hacking group known as Evil Corp.
The two sources, who spoke on the condition of anonymity as they are not authorized to speak to the press, told TechCrunch that Garmin was trying to bring its network back online after the ransomware attack. One of the sources confirmed that the WastedLocker ransomware was to blame for the outage.
One other news outlet [Bleeping Computer] appeared to confirm that the outage was caused by WastedLocker. [Zack Whittaker, TechCrunch]
The company hasn’t said whether or not they paid to have the ransomware removed, but said: “We do not expect any material impact to our operations or financial results because of this outage.”
Garmin’s system status page can be checked for further updates on the recovery, though the company says everything should be back to normal in the coming week.
Check out our prior smart home cybersecurity updates:
- June 2019: Linksys Smart WiFi router vulnerability and Android pre-installed backdoor
- July 2019: Website drive-by attacks on home routers
- August 2019: VxWorks and Google Nest Cam IQ Indoor vulnerabilities
- September 2019: SMS-based attacks and major router vulnerabilities
- October 2019: What is Gafgyt malware?
- November 2019: What is Light Commands?
- December 2019: Blink camera and Ruckus router vulnerabilities
- January 2020: Ring doorbell privacy concerns
- March 2020: Work From Home edition
- April 2020: Malware stats amid COVID-19
- May 2020: Brand impersonation spear phishing attacks and Nest security update
- June 2020: NETGEAR zero-day vulnerabilities, Ripple20, and Shalyer malware variant